Can you decrypt AES

Isabella Wilson
Published Mar 14, 2026
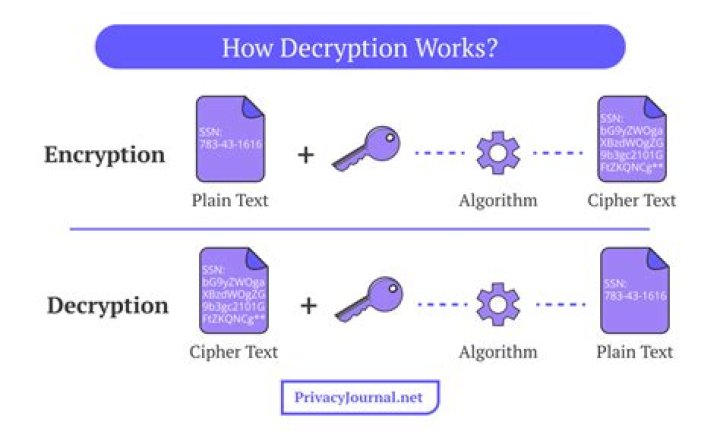
Only those who have the special key can decrypt it. AES uses symmetric key encryption, which involves the use of only one secret key to cipher and decipher information.
Can I decrypt AES without key?
2 Answers. No, you cannot decrypt without knowing the key. What would the point of encryption be if anyone could decrypt the message without even having the key? If this is intended to hide data from a local user, then pretty much the best you can is obfuscate the data.
Can you decrypt AES 256?
If the key was securely and randomly generated, and all copies of the key have been destroyed, it is considered impossible to decrypt the data based on what we know. Brute-force attacks on a 256-bit key are impossible (physically impossible, actually).
How do I decrypt an AES password?
1 Answer. You need to know more than just the password’s AES string. You need to know which AES it was encrypted with, for example, and the key or password used to encrypt it. And then call mysql with $DECODED as the password argument instead.Can AES be cracked?
In the end, AES has never been cracked yet and is safe against any brute force attacks contrary to belief and arguments. However, the key size used for encryption should always be large enough that it could not be cracked by modern computers despite considering advancements in processor speeds based on Moore’s law.
Can you decrypt a message without knowing K?
No, not with the current hardware if a good encryption method was used and the key (password) was long enough. Unless there is a flaw in the algorithm and that you know it, your only option is to brute force it which might takes hundred of years.
How long would it take to decrypt AES 256?
With the right quantum computer, AES-128 would take about 2.61*10^12 years to crack, while AES-256 would take 2.29*10^32 years.
How do I know my AES key length?
2 Answers. There is no relationship between key size and block size in AES , because it it not a simple XOR . Block size is always 128 bits, but key size can be 128, 192, and 256 bits based on algorithm rounds.Do you need the IV to decrypt AES?
After the first block is decrypted, you still have an intermediate value which has been XORed with the plaintext — without this, you have little hope of recovering the plaintext. However, you do not need the IV to decrypt subsequent blocks.
How do I decrypt AES encryption in Python?And that is all there is to encrypting and decrypting a file using AES in python. We need to generate or obtain a key, create the initialization vector and write the original file size followed by the IV into the output file. This is followed by the encrypted data. Finally decryption does the same process in reverse.
Article first time published onDoes 512-bit encryption exist?
There isn’t a single 512-bit symmetric key cipher in common public use. The whirlpool hash function, which is based on AES, returns a 512-bit digest, but that’s not the same thing as a 512-bit AES cipher. The common comparison with RSA is that a 128 bit symmetric key corresponds to about 3000 bit RSA.
How long would it take to crack 512-bit encryption?
The cost and time required to break 512-bit RSA encryption keys has plummeted to an all-time low of just $75 and four hours using a recently published recipe that even computing novices can follow.
How hard is it to break 256-bit encryption?
In today’s level of technology, it is still impossible to break or brute-force a 256-bit encryption algorithm. In fact, with the kind of computers currently available to the public it would take literally billions of years to break this type of encryption.
Has 256 bit encryption been cracked?
AES-256 (Advacnce Encryption Standard) with 256 bit key is the most advance cryptographic algorithm till date and not have been broken yet. But it is not far away in near future, it will be no longer be secure with the recent developments made into quantum computers.
Can quantum computers break AES 128?
In the case of asymmetric encryption algorithms (like RSA), quantum computing completely breaks them. … Grover’s algorithm decreases the effective key length of a symmetric encryption algorithm by half, so AES-128 has an effective key space of 2^64 and AES-256 has an effective key space of 2^128.
Has AES 128 been broken?
AES, which typically uses keys that are either 128 or 256 bits long, has never been broken, while DES can now be broken in a matter of hours, Moorcones says. AES is approved for sensitive U.S. government information that is not classified, he adds.
Can you Bruteforce AES 256?
On average, to brute-force attack AES-256, one would need to try 2255 keys. (This is the total size of the key space divided by 2, because on average, you’ll find the answer after searching half the key space.) So the time taken to perform this attack, measured in years, is simply 2255 / 2,117.8 trillion.
Can you brute force encryption?
Brute-force attacks are fairly simple to understand, but difficult to protect against. Encryption is math, and as computers become faster at math, they become faster at trying all the solutions and seeing which one fits. These attacks can be used against any type of encryption, with varying degrees of success.
How long to brute force 1024 bit key?
Kaspersky Lab is launching an international distributed effort to crack a 1024-bit RSA key used by the Gpcode Virus. From their website: We estimate it would take around 15 million modern computers, running for about a year, to crack such a key.
Can you decrypt encrypted?
For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required.
Can you decrypt encryption?
If you’ve encrypted your files with EFS, then you can easily decrypt them from the Properties section. Right-click on the encrypted file and select Properties. In the General tab, select Advanced. Now, uncheck the Encrypt contents to secure data radio box and click on OK.
Is it possible to decrypt a password?
Passwords aren’t typically encrypted, they’re hashed with a one-way function. “One-way” meaning they can’t be “decrypted” or reversed. To authenticate with a website, the user supplies the password again, it’s hashed again, and the result is compared to the stored hash. If they match, you’re allowed in.
Is IV secret?
In cipher-block chaining mode (CBC mode), the IV need not be secret, but must be unpredictable (In particular, for any given plaintext, it must not be possible to predict the IV that will be associated to the plaintext in advance of the generation of the IV.) … Additionally for the OFB mode, the IV must be unique.
Why is IV not a secret?
IV usually does not need to be secret, However, in most cases, it is important that an initialization vector is never reused under the same key. Wikipedia: An initialization vector has different security requirements than a key, so the IV usually does not need to be secret.
What information will be leaked if IV is reused?
For CBC and CFB, reusing an IV leaks some information about the first block of plaintext, and about any common prefix shared by the two messages. You don’t need to keep the IV secret, but it must be random and unique. If you had to keep the IV secret, it would be part of the key.
How many rounds does the AES 256 perform?
The three AES varieties are also distinguished by the number of rounds of encryption. AES 128 uses 10 rounds, AES 192 uses 12 rounds, and AES 256 uses 14 rounds.
Is AES a block cipher?
The Advanced Encryption Standard (AES) is a symmetric block cipher chosen by the U.S. government to protect classified information. AES is implemented in software and hardware throughout the world to encrypt sensitive data.
Is AES 128 still secure?
The difference between cracking the AES-128 algorithm and AES-256 algorithm is considered minimal. Whatever breakthrough might crack 128-bit will probably also crack 256-bit. In the end, AES has never been cracked yet and is safe against any brute force attacks contrary to belief and arguments.
What is IV in AES Python?
The input to the encryption processes of the CBC, CFB, and OFB modes includes, in addition to the plaintext, a data block called the initialization vector (IV), denoted IV. The IV is used in an initial step in the encryption of a message and in the corresponding decryption of the message.
What is IV in AES encryption?
An initialization vector (IV) is an arbitrary number that can be used along with a secret key for data encryption. This number, also called a nonce, is employed only one time in any session.
How does AES work in Python?
- Lets take a quick walk through the constructor, it receives a key which can be of any length. …
- The __pad method receives the plain_text to be encrypted and adds a number bytes for the text to be a multiple of 128 bits.