What are the types of vulnerability assessments

Andrew White
Published Mar 05, 2026
Network-based scans.Host-based scans.Wireless scans.Database scans.Application scans.
What are the 4 main types of security vulnerability?
- Network Vulnerabilities. These are issues with a network’s hardware or software that expose it to possible intrusion by an outside party. …
- Operating System Vulnerabilities. …
- Human Vulnerabilities. …
- Process Vulnerabilities.
What is vulnerability assessment list out the types of vulnerability assessment?
Types of vulnerability assessments Network-based scans are used to identify possible network security attacks. This type of scan can also detect vulnerable systems on wired or wireless networks. Host-based scans are used to locate and identify vulnerabilities in servers, workstations or other network hosts.
What are the different types of vulnerability?
According to the different types of losses, the vulnerability can be defined as physical vulnerability, economic vulnerability, social vulnerability and environmental vulnerability.What are four types of vulnerability assessments A cyber security analyst or engineer can perform?
A vulnerability assessment is an examination of vulnerabilities in IT systems at a certain point in time with the goal of detecting system flaws before hackers may exploit them. Security assessments come in four types: application scans, network or wireless assessment, database assessment, and host assessment.
Which of the following are common types of security vulnerabilities?
- Missing data encryption.
- OS command injection.
- SQL injection.
- Buffer overflow.
- Missing authentication for critical function.
- Missing authorization.
- Unrestricted upload of dangerous file types.
- Reliance on untrusted inputs in a security decision.
What is security vulnerability assessment?
A vulnerability assessment is a systematic review of security weaknesses in an information system. It evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed.
What are the five types of vulnerability assessment?
- Network and Wireless Assessment. Identifies possible vulnerabilities in network security. …
- Host Assessment. …
- Database Assessment. …
- Application Scans. …
- Determine Critical and Attractive Assets. …
- Conduct Vulnerability Assessment. …
- Vulnerability Analysis and Risk Assessment. …
- Remediation.
What are the elements of vulnerability?
Vulnerability can be divided into four main areas: physical, social, economic and system-depending on the class of elements at risk being considered.
What are the different types of vulnerabilities in cyber security?- System Misconfigurations. …
- Out-of-date or Unpatched Software. …
- Missing or Weak Authorization Credentials. …
- Malicious Insider Threats. …
- Missing or Poor Data Encryption. …
- Zero-day Vulnerabilities. …
- Vulnerability Detection. …
- Cyber Security Vulnerability Assessment.
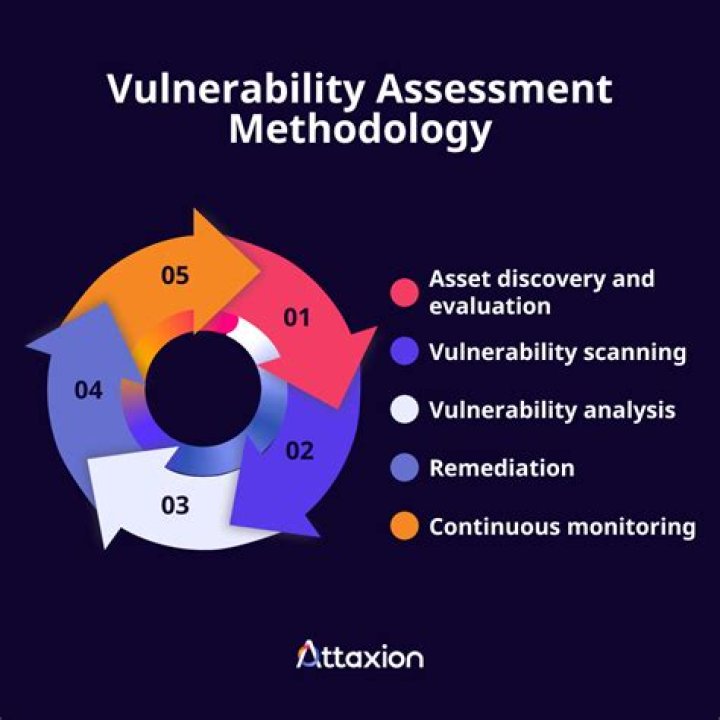
What is vulnerability assessment methodology?
Vulnerability assessment is the process of defining, identifying, classifying, and prioritizing vulnerabilities in systems, applications, and networks. It provides an organization with the needed visibility into the risks that exist concerning external threats designed to take advantage of vulnerabilities.
What is the first step in a vulnerability assessment?
1. Initial Assessment. Identify the assets and define the risk and critical value for each device (based on the client input), such as a security assessment vulnerability scanner. It’s important to identify at least the importance of the device that you have on your network or at least the devices that you’ll test.
What is an advanced vulnerability assessment?
While the process of vulnerability assessment checks an organization for potential vulnerabilities, specifically technical ones, advanced vulnerability assessments go further to actually check whether an organization is truly vulnerable to exploit. …
What is vulnerability management in cyber security?
Vulnerability management is the process of identifying, evaluating, treating, and reporting on security vulnerabilities in systems and the software that runs on them. This, implemented alongside with other security tactics, is vital for organizations to prioritize possible threats and minimizing their “attack surface.”
Which of the following is best used with vulnerability assessments?
Explanation: White box testing provides the penetration testers information about the target network before they start their work. This information can include such details as IP addresses, network infrastructure schematics and the protocols used plus the source code.
Which of the following are examples of vulnerabilities?
- A weakness in a firewall that lets hackers get into a computer network.
- Unlocked doors at businesses, and/or.
- Lack of security cameras.
What are the most common security vulnerabilities for broadcasters?
The most common vulnerability was encryption misconfiguration, accounting for one third (33.42%) of those identified, followed by unnecessary features at just over a quarter (26.53%).
What are the causes of vulnerability?
Other causes includes; lack of access to information and knowledge, lack of public awareness, limited access to political power and representation (political vulnerability), (Aysan,1993). When people are socially disadvantaged or lack political voice, their vulnerability is exacerbated further.
What is the concept of vulnerability?
Vulnerability has been defined as the degree to which a system, or part of it, may react adversely during the occurrence of a hazardous event. … (2) Soft resilience : the ability of systems to absorb and recover from the impact of disruptive events without fundamental changes in function or structure.
What are the vulnerabilities of risk assessment?
In essence, risk assessment involves looking outside of an organization to determine what threats exist that could potentially lead to problems, while vulnerability assessment involves looking inside the organization for structural flaws and weaknesses.
What are the three main areas of vulnerabilities for security?
- Faulty defenses.
- Poor resource management.
- Insecure connection between elements.
How many steps are in the vulnerability assessment phase?
There are 8 steps to performing a network security vulnerability assessment, which includes: conducting risk identification and analysis, developing vulnerability scanning policies and procedures, identifying the type of vulnerability scan, configuring the scan, performing the scan, evaluating risks, interpreting the …
Which is usually the second step in vulnerability assessment?
The second step in a vulnerability assessment is to determine the assets that need to be protected. Determining vulnerabilities often depends on the background and experience of the assessor. … Vulnerability scanning should be conducted on existing systems and particularly as new technology equipment is deployed.
What is done after a vulnerability assessment?
The final report from a VA should indicate where potential security gaps exist. The next step in the VMP process is to verify the realistic risk of each one and then prioritise them based on severity. After that, the team running the VMP must determine a mitigation tactic for each identified vulnerability.
What is a threat assessment plan?
Threat assessment is intended to prevent violence and involves both assessment and intervention. Threat assessment involves determining whether a student poses a threat of violence (they have intent and means to carry out the threat). A threat is an expression of intent to physically or sexually harm someone.
What are the four steps to vulnerability management?
A vulnerability management process can vary between environments, but most should follow four main stages—identifying vulnerabilities, evaluating vulnerabilities, treating vulnerabilities, and finally reporting vulnerabilities. Typically, a combination of tools and human resources perform these processes.
What are common methods for managing vulnerabilities?
- Asset discovery.
- Data classification.
- Intrusion detection.
- Privilege access management.
- Threat detection and response.
- SIEM and log data correlation.
- Compliance auditing and reporting.
What is Falcon spotlight?
Falcon Spotlight: Scanless Vulnerability Management As part of an integrated platform that prevents exploits and post-exploit activity, Falcon Spotlight™ allows you to research common vulnerabilities and exposures (CVEs) to examine threat actor profiles and targets.