What is it hygiene

Isabella Wilson
Published May 08, 2026
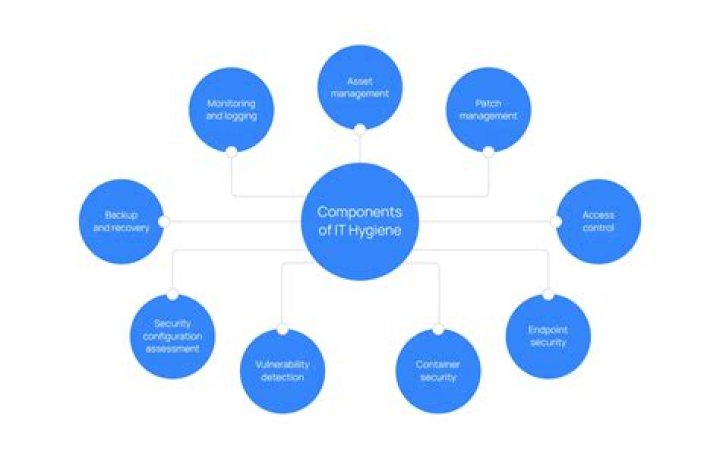
Cyber hygiene refers to fundamental cybersecurity best practices that an organization’s security practitioners and users can undertake. As you have personal hygiene practices to maintain your own health, cyber hygiene best practices help protect the health of your organization’s network and assets.
What do you mean by cyber hygiene?
Cyber hygiene refers to fundamental cybersecurity best practices that an organization’s security practitioners and users can undertake. As you have personal hygiene practices to maintain your own health, cyber hygiene best practices help protect the health of your organization’s network and assets.
What are examples of good cyber hygiene?
- Step 1: Install reputable antivirus and malware software. …
- Step 2: Use network firewalls. …
- Step 3: Update software regularly. …
- Step 4: Set strong passwords. …
- Step 5: Use multi-factor authentication. …
- Step 6: Employ device encryption. …
- Step 7: Back up regularly. …
- Step 8: Keep your hard drive clean.
Why cyber hygiene is important?
Creating a routine around cyber hygiene helps ensure a system’s health by enabling practices that continually help prevent cybercriminals from causing security breaches, installing malware or stealing personal information. Having proper cyber hygiene also ensures better incident response if a successful attack occurs.Why is net hygiene important now a days?
Defining Cyber Hygiene This means protecting and maintaining systems and devices using cybersecurity best practices for every device that can connect to the internet. By being proactive and vigilant to enhance your cyber hygiene, your organization can better protect against cyber threats now and in the future.
How can digital hygiene be improved?
Strong passwords still matter. Change personal wifi names to something less identifiable. Change the passwords on wifi routers to something more complex and hard to crack by adding numbers and special characters to it. Change the default passwords of personal smart devices connected to your home internet.
What are the common cyber hygiene problems?
Common cyber hygiene problems include: Loss of data: Hard drives, online cloud storage and SaaS apps that store sensitive data that isn’t backed up or maintained can be vulnerable to hacking, corruption, data leaks, and data breaches. To learn how to fix this problem, read our guide on data loss prevention.
What is computer ransomware?
Share: Ransomware is malware that employs encryption to hold a victim’s information at ransom. A user or organization’s critical data is encrypted so that they cannot access files, databases, or applications. A ransom is then demanded to provide access.What is operational hygiene?
Operational hygiene in practice. In the context of firefighting, this means not only protection against harmful substances during deployment, primarily through respiratory protection and personal protective equipment (PPE), but also protection against substances that are hazardous to health after deployment.
What is the difference between Internet security and Internet safety?So, put simply: cyber security means protecting data and information networks. cyber safety means protecting users from harmful online content.
Article first time published onWhat are good computer security habits?
Habit One: Practise good passwords Do not share passwords with others (no matter how much you like them) Do not write passwords down on paper – if you do, place the paper in a safe, lockable place. Do not use the same password for multiple accounts. Create passwords using 3 or more random words.
What does DDoS mean?
DDoS stands for Distributed Denial of Service, and it’s a method where cybercriminals flood a network with so much malicious traffic that it cannot operate or communicate as it normally would. This causes the site’s normal traffic, also known as legitimate packets, to come to a halt.
What is a Trojan hack?
Trojans can use the victim computer to attack other systems using Denial of Services. … Trojans can encrypt all your files and the hacker may thereafter demand money to decrypt them. These are Ransomware Trojans. They can use your phones to send SMS to third parties.
Is ransomware a virus or worm?
Simply put, ransomware is a subset of malware. Malware attacks usually come in the form of a computer virus or worm. A virus piggybacks on something like a document, spreadsheet or e-mail, whereas a worm is a more active attack.
Can antivirus detect ransomware?
As you see, antivirus solutions can detect some ransomware attacks but are unable to completely prevent ransomware from infecting your system. No AV is even close to protecting you from 100% of ransomware attacks.
What are the types of computer crime?
- Email and internet fraud.
- Identity fraud (where personal information is stolen and used).
- Theft of financial or card payment data.
- Theft and sale of corporate data.
- Cyberextortion (demanding money to prevent a threatened attack).
- Ransomware attacks (a type of cyberextortion).
Is Internet safe or not?
The internet can be a dangerous neighborhood for everyone, but children and teens are especially vulnerable. … Although cyber security software can help protect against some threats, the most important safety measure is open communication with your children.
What is social en?
Social engineering is the art of manipulating people so they give up confidential information. … Criminals use social engineering tactics because it is usually easier to exploit your natural inclination to trust than it is to discover ways to hack your software.
How can I improve my cybersecurity habits?
- Make them long and strong.
- Never reveal your password to anyone.
- Use different passwords for different accounts.
- Use different passwords for work and non-work activities.
- Click “no” when websites or apps ask to remember your password.
What are the three necessary components to develop positive security habits?
- Create a strong password. Use a strong password that is unique for each device or account. …
- Consider using a password manager. …
- Use multi-factor authentication, if available. …
- Use security questions properly. …
- Create unique accounts for each user per device.
What are the signs of being DDoSed?
- Slow access to files, either locally or remotely.
- A long-term inability to access a particular website.
- Internet disconnection.
- Problems accessing all websites.
- Excessive amount of spam emails.
Can your phone get DDoSed?
And smartphones aren’t serving things in the same way as real servers. Sure, they are listening on some ports, and responding in some way. So, yes, they can technically be DDoSed.
Does VPN stop DDoS?
Generally speaking, yes, VPNs can stop DDoS attacks. … With a hidden IP address, DDoS attacks can’t locate your network, making it much harder to target you. Additionally, VPNs encrypt web traffic, creating a tunnel between your computer and network, thus hiding activity from your internet service provider (ISP).
What is the most famous virus attacks in the world?
- ILOVEYOU. In May 2000, the ILOVEYOU virus shut down the email servers of several major corporations, including Microsoft and Ford. …
- Mydoom. …
- Storm Worm Trojan Horse. …
- CryptoLocker. …
- WannaCry.
What is the most damaging computer virus?
1. Mydoom – $38 billion. The worst computer virus outbreak in history, Mydoom caused estimated damage of $38 billion in 2004, but its inflation-adjusted cost is actually $52.2 billion. Also known as Novarg, this malware is technically a “worm,” spread by mass emailing.
What is a worm hack?
Definition: The worm is a standalone malicious program which spreads from computer to computer, but unlike a virus, it has the capability to travel without any human action. … Often, it uses a computer network to spread itself, relying on security failures on the target computer to access it.
What is a virus Mcafee?
A virus is a specific type of malware that self-replicates by inserting its code into other programs.
Is ransomware same as malware?
Ransomware has similar attributes to malware, and can actually be classified as a subset of malware. While ransomware allows attackers to gain full control of your systems just like malware, this one will only restrict access to the personal and confidential files until a ransom is paid (hence the name).
What is the difference between ransomware and Trojan?
Trojan Horse is a form of malware that capture some important information about a computer system or a computer network. Ransomware is a form of malware designed to block access from system until a ransom fee is paid.