Why is public key encryption better than private key encryption

Isabella Wilson
Published Mar 17, 2026
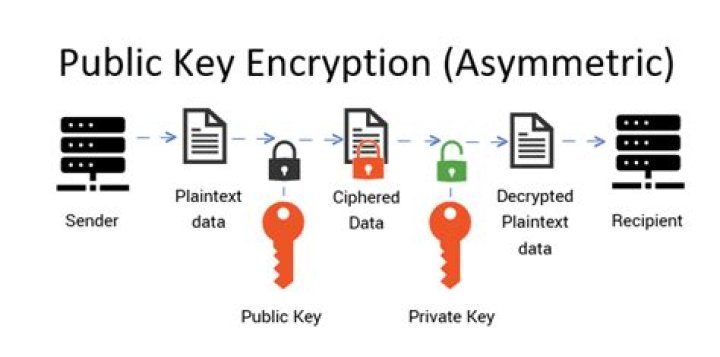
Private Key is used to both encrypt and decrypt the data and is shared between the sender and receiver of encrypted data. The public key is only used to encrypt data and to decrypt the data, the private key is used and is shared. The private key mechanism is faster. The public key mechanism is slower.
Why is public key encryption better?
Symmetric encryption allows two or more parties to securely exchange information with one another so long as all parties can securely share the same secret key (used to encrypt and decrypt the information). … Messages encrypted with the public key can only be decrypted with the private key and vice versa.
What is the difference between a private key and public key?
One key (public key) is used for encrypt the plain text to convert it into cipher text and another key (private key) is used by receiver to decrypt the cipher text to read the message. 1. Private key is faster than public key.
Why is public key encryption deemed more secured compared to private key encryption?
The primary benefit of public key cryptography is increased data and identity security at scale. What makes the process secure is that the private key is kept secret by its owner, and no one is ever required to reveal or share a private key.How good is public key encryption?
Standard public-key encryption is secure as long as an attacker knows nothing other than the public key. But financial institutions and other large organizations seek security against more sophisticated attacks, called chosen-ciphertext attacks (CCAs), in which the attacker also has examples of successful decryption.
Do you encrypt with public or private key?
Encryption is done with public key only, since the key is public, and only the holder of private key can decrypt it.
Does public key encryption guarantee integrity?
Benefits of public key cryptography It enables organizations to maintain data confidentiality and integrity, resulting in more robust information security. Apart from encryption strength, public key cryptography also enables users to verify digital identities while ensuring non-repudiation.
What is difference between private and public SSH?
The private key is secret, known only to the user, and should be encrypted and stored safely. The public key can be shared freely with any SSH server to which the user wishes to connect.What are the advantages and disadvantages of public key encryption?
- Security is easy as only the private key must be kept secret.
- Maintenance of the keys becomes easy being the keys (public key/private key) remain constant through out the communication depending on the connection.
Public key encryption is extremely useful for establishing secure communications over the Internet (via HTTPS). A website’s SSL/TLS certificate, which is shared publicly, contains the public key, and the private key is installed on the origin server – it’s “owned” by the website.
Article first time published onWhat is the difference between conventional and public key encryption?
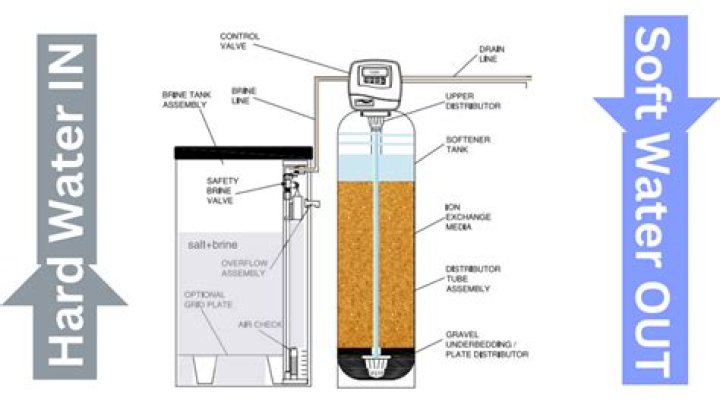
Definition. – Conventional encryption, also called as symmetric encryption or single-key encryption is a type of cryptographic system which uses a single key to both encrypt the message and decrypt it. … The public key is used to encrypt a message and the private key is then used to decrypt the message.
Is private key used for encryption or decryption?
Unlike symmetric key algorithms that rely on one key to both encrypt and decrypt, each key performs a unique function. The public key is used to encrypt and the private key is used to decrypt.
How public key and private key is used in encryption and decryption of an important message?
In public key cryptography, every public key matches to only one private key. Together, they are used to encrypt and decrypt messages. If you encode a message using a person’s public key, they can only decode it using their matching private key.
Why is public key cryptography slow?
The first method for public key cryptography, developed around 1975, was based on raising very large numbers (thousands of bits) to very large powers modulo another very large number. It is slow because arithmetic using very large numbers is slow.
What is the main disadvantage of public key encryption?
A disadvantage of using public-key cryptography for encryption is speed. There are many secret-key encryption methods that are significantly faster than any currently available public-key encryption method. Nevertheless, public-key cryptography can be used with secret-key cryptography to get the best of both worlds.
What are the benefits of PKI?
- minimise fraud by authenticating the identity of people via the Internet.
- provide privacy of messages by minimising the risk that they can be read in transit, or by anyone, other than the intended recipient.
How are public and private keys are used for confidentiality integrity and authenticity?
By using a public and private key for encryption and decryption, recipients can be confident that the data is what the sender says it is. The recipient is assured of the confidentiality, integrity and authenticity of the data. … The only way to decrypt Alice’s private key is with her public key, which Bob can access.
Can a public key decrypt a private key?
Yes, a message which has encrypted using private key can be decrypted using the public key. In the digital signature, a person encrypts the hash of the data with his private key. Anyone can decrypt the same with the available public key of the person and verify the authenticity of the data.
How does public key cryptography provides integrity?
The most obvious application of a public key encryption system is for encrypting communication to provide confidentiality – a message that a sender encrypts using the recipient’s public key which can be decrypted only by the recipient’s paired private key.
Are public keys safe to share?
Yes. It is safe to share and it is the purpose of the public key. In asymmetric cryptography, public and private key pair is generated and Public key is published in the open directory whereas the Owner always retains private key.
Can private key used for encryption?
Private keys may be protected with a password, encrypted or hashed for security — or all three. Key exchange. The private key is used to decrypt, as well as to encrypt, so using it for symmetric encryption requires a key exchange to share that key securely with trusted parties authorized to exchange secured data.
Why does CA need to encrypt the hash message with its private key?
Encrypting using the private key is therefore a way of authenticating data. Now, anyone wanting data from Bob can download a copy of the encrypted document and a copy of his public key. They decrypt the file using the public key and can satisfy themselves the data is genuine.
What are the main differences advantages and disadvantages of symmetrical and asymmetrical encryption?
The main advantage of symmetric encryption over asymmetric encryption is that it is fast and efficient for large amounts of data; the disadvantage is the need to keep the key secret – this can be especially challenging where encryption and decryption take place in different locations, requiring the key to be moved …
How public key encryption overcomes the problem?
In asymmetric or public key, cryptography there is no need for exchanging keys, thus eliminating the key distribution problem. The primary advantage of public-key cryptography is increased security: the private keys do not ever need to be transmitted or revealed to anyone.
What is an important disadvantage of using public key algorithm compared to symmetric algorithm?
What is an important disadvantage of using a public key algorithm compared to a symmetric algorithm? … A symmetric algorithm is a faster process. A symmetric algorithm provides nonrepudiation of delivery. A symmetric algorithm is more diffi cult to implement.
When we use two different keys namely a private key and a public key it is known as?
Asymmetric cryptography, also known as public-key cryptography, is a process that uses a pair of related keys — one public key and one private key — to encrypt and decrypt a message and protect it from unauthorized access or use.
How does public and private key work in SFTP?
The user’s Public & Private Keys are a pair of keys used to authenticate a client when it connects to an SFTP server. The user’s private key is kept secret and stored locally on the user’s PC while the user’s public key is uploaded and registered on the SFTP server the user connects to.
What are the two different uses of public key cryptography related to key distribution?
In public key cryptography, we use two keys: one for encryption and the second for decryption. We can distribute the public key everywhere without compromising the private key. A user will use his friend’s public key to encrypt the message.
Why public-key encryption is important in e commerce?
As a foundation for E-commerce security, it enhances the security service functionalities, such as authentication, confidentiality, integrity, and non-repudiation of the systems. Encrypting the file only solves the problem of confidentiality of the transmitted information.
Why is public key slower than private key?
There are three efficiency issues to discuss here: CPU, network bandwidth, and functionalities. The “moral” reason of public key encryption being slower than private key encryption is that it must realize a qualitatively harder feature: to be able to publish the encryption key without revealing the decryption key.
What are the advantages and disadvantages of asymmetric cryptography?
- It allows message authentication. …
- It is convenient. …
- It allows for non-repudiation. …
- It detects tampering. …
- It is a slow process. …
- Its public keys are not authenticated. …
- It risks loss of private key, which may be irreparable. …
- It risks widespread security compromise.